Background
The client is a Managed IT Services Provider (MSP) based in Australia, specializing in cybersecurity and business resilience. For a company that advises other businesses on risk mitigation, maintaining the integrity of their own digital presence is not just an operational requirement, it is critical to their brand reputation. They needed a technical support partner capable of responding to security threats with the same speed and rigor they promise their own clients.
Rapid Response to a Malware Injection
When the client’s leadership team reported a critical security breach late on a Sunday night, the goal wasn’t just to “fix” the website, it was to contain the threat immediately and provide a forensic explanation to satisfy their internal security protocols.
Pronto Marketing’s technical support team initiated an emergency response within minutes of the report. Over the next 40 minutes, the team executed a coordinated cleanup with the hosting partner, locked down unauthorized access, and traced the breach to its source to prevent recurrence.
The Challenge: A “Fake reCAPTCHA” Hijacking
On November 9, 2025, at 10:39 PM, the client reported that their website was displaying a fraudulent pop-up across all pages.
This was a sophisticated malware attack known as a “fake reCAPTCHA,” designed to trick visitors into clicking a verification button that actually executes a malicious command on their device.
The situation presented immediate critical risks:
- Visitor Safety: Any client or prospect visiting the site was at risk of downloading information-stealing malware.
- Reputation Damage: As an IT provider, hosting active malware would directly undermine trust in their security services.
- Compromised Access: The presence of the malware indicated that an attacker had successfully breached the website’s backend.
The Solution: A Four-Step Forensic Containment
Pronto Marketing’s Technical WordPress Support team moved from initial report to full resolution in approximately 40 minutes. Here is how the response unfolded:
1. Identification and Immediate Sanitation
Three minutes after the ticket was logged, a Pronto engineer began the investigation. Recognizing the severity of the “fake reCAPTCHA” signature, the team engaged hosting partner (Kinsta) to conduct a server-side scan.
- Action: Identified and removed a malicious script hiding in the database.
- Verification: Confirmed the malicious overlay was gone and the site was clean.
2. Locking Down Access and Credentials
Removing the malware was only the first step; the team had to ensure the attacker could not return.
- Forced Resets: Passwords were reset for all administrator users and SFTP accounts.
- User Audits: The team provided a list of all active users to the client, identifying specific accounts belonging to third-party marketing vendors that were no longer needed.
- Removal: Upon client approval, these third-party accounts (e.g., ads@…, admin@mogrify…) were permanently deleted.
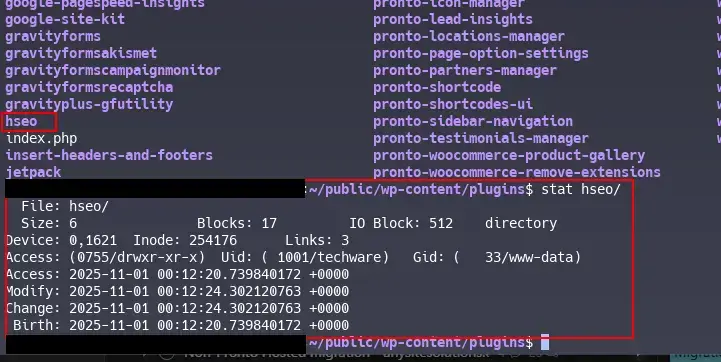
3. Forensic Root Cause Analysis
To answer the client’s request for a “root cause,” Pronto engineers synchronized the infected state to a staging environment to trace the entry point safely.
- The Findings: Logs revealed that a user account named sarahm (associated with an external vendor) had uploaded a zip file named hseo.zip.
- The Mechanism: This zip file contained a custom PHP script that enqueued the malicious JavaScript responsible for the attack.
- The Verdict: The attacker had compromised the credentials of a third-party vendor and used the standard “Add Plugin” feature to upload the malware.
4. Strategic Hardening
To close this vulnerability permanently, Pronto implemented a stricter security configuration.
- Configuration Change: The team enabled disallow_file_mod, a setting that disables the ability to install or edit plugins and themes directly from the WordPress dashboard.
- Impact: Even if a user account is compromised in the future, the attacker cannot upload malicious zip files through the admin interface.
The Result: Security Restored and Risks Mitigated
The rapid response converted a potential reputational crisis into a demonstration of effective incident management.
A 40-Minute Resolution Time: Between the initial report at 10:39 PM and the confirmation of a clean site at 11:20 PM, the site was fully restored, minimizing exposure to the client’s traffic.
Elimination of Third-Party Vulnerabilities: By auditing and removing unused vendor accounts, the attack surface was significantly reduced. The compromised account used for the injection was permanently removed.
Transparent Forensic Reporting: The client received a detailed “Post-Mortem” explanation, allowing their leadership to align the incident with their internal risk messaging and reassure their own stakeholders.
Future-Proofed Security: With the new configuration blocking dashboard uploads, the specific method used by the attacker (uploading a fake plugin) was rendered impossible for future attempts.